I had an assignment today that required me to block a port on stbkp01 on which Apache HTTP was running (8082) and allow all connections to another port on which Nginx was running (8096). After inserting two rules in the Netfilter ‘filter’ table’s INPUT chain to block both TCP and UDP on the port Apache was running on (since those are the two protocols that use ephemeral ports) I marked the exercise as finished but was told I had failed the exercise.
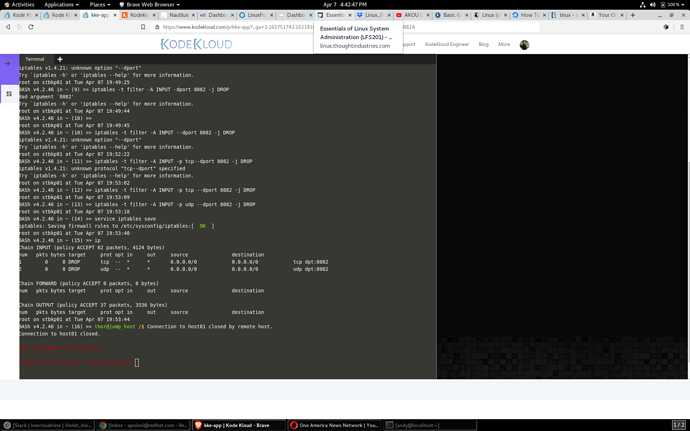
No filter table INPUT rules were required to allow connections to the Nginx port given the default policy for the INPUT chain was set to ACCEPT (see attached screenshot). When I submitted the assignment and was told I had failed it mentioned the fact that there were no INPUT chain rules for the Nginx port, however those weren’t required given the chain’s default policy of ACCEPT.
I might suggest if you want to have these kinds of assignments you might want to be more specific about what exactly you want to see in the Netfilter config (i.e., create the appropriate INPUT rules regardless of the filter INPUT chain’s default policy) or appropriately set the default policy to DROP so that the rules are required.